Trezor Login: Secure Access to Your Crypto Wallet
Learn how to log in safely to your Trezor wallet, avoid phishing attacks, and manage your assets securely using Trezor Suite.
Why “Trezor Login” Matters
The phrase Trezor Login is one of the most common searches by crypto holders. But here’s the truth: there is no traditional “username + password” login system with Trezor. Instead, your hardware wallet and PIN act as your login credentials, giving you direct access to your private keys without ever exposing them online.
That’s why understanding the right way to log in with Trezor is essential for protecting your digital wealth.
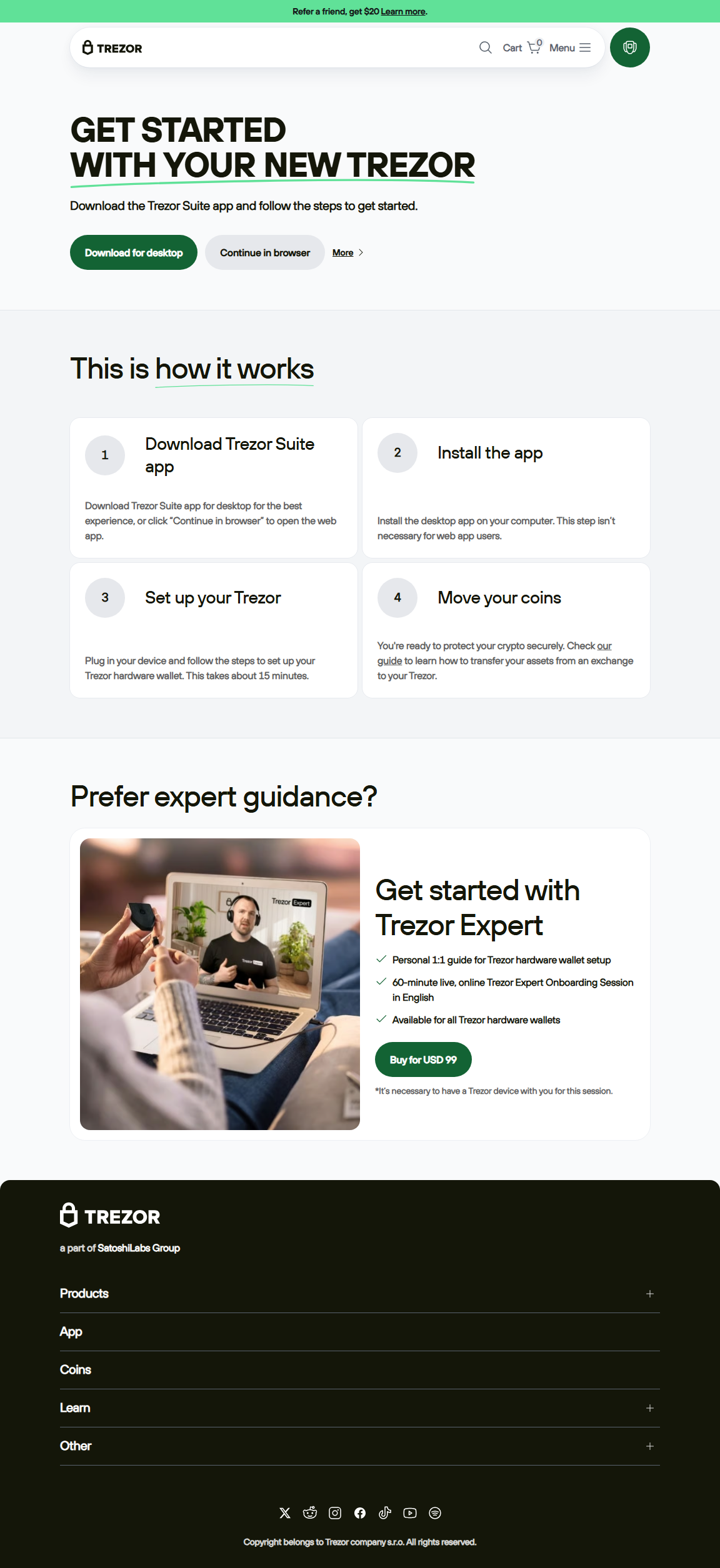
Step-by-Step: How to Log In with Trezor
- Open Trezor Suite: Download the official desktop or web app from Trezor.io.
- Connect Your Device: Plug in your Trezor One or Model T using the USB cable.
- Enter Your PIN: A randomized keypad appears on your device. Enter the correct sequence on your computer screen.
- Optional – Enter Passphrase: If enabled, add a passphrase for hidden wallets or enhanced security.
- Access Your Dashboard: Once verified, you can view balances, manage accounts, send/receive crypto, and more.
⚠️ Security Tips for Trezor Login
- Always download Trezor Suite from the official website — never third-party links.
- Never enter your recovery seed during login. Trezor will never ask for it online.
- Bookmark the official site (trezor.io) to avoid phishing attacks.
- Check the device screen for address verification when sending funds.
Trezor Login vs. Exchange Login
| Feature | Trezor Login | Exchange Login |
|---|---|---|
| Authentication | PIN + Device + (Optional) Passphrase | Username + Password + 2FA |
| Private Key Storage | Offline in hardware wallet | Stored on exchange servers |
| Risk | Minimal (device theft risk only) | High (exchange hacks, leaks) |
Analogy: Logging into Trezor is Like Unlocking a Safe
Think of your Trezor as a bank-grade safe. Instead of logging in with a weak password, you unlock it with a unique combination (your PIN) and an optional extra layer (passphrase). Unlike an online bank account, the “safe” never leaves your hands — your crypto keys stay inside your device.
Advanced Trezor Login Tips
- Hidden Wallets: Use different passphrases to create decoy wallets.
- Tor Connection: Enable Tor in Trezor Suite for extra privacy.
- Multiple Devices: You can log in with different Trezor devices to diversify holdings.
- Firmware Updates: Keep your device updated to avoid login or connectivity issues.
Frequently Asked Questions about Trezor Login
1. Can I log in to Trezor without the device?
No. Your Trezor hardware wallet is essential. Without it, there is no way to access your private keys.
2. What if I forget my PIN?
You can reset the device, but you’ll need your recovery seed to restore your wallet. Without the seed, funds are unrecoverable.
3. Do I need an internet connection for Trezor Login?
Yes, to use Trezor Suite. But your private keys never leave the device — they remain offline and safe.
Final Thoughts
The phrase Trezor Login might suggest a traditional account system, but in reality, it’s much safer. Your device is the login key, your PIN is the lock, and your recovery seed is the ultimate backup. By always using the official Trezor Suite, you keep your assets safe while enjoying full control over your digital wealth.